Privacy Canada is community-supported. We may earn a commission when make a purchase through one of our links. Learn more.
Five Eyes Explained (FVEY) – Big Brother Is Watching you

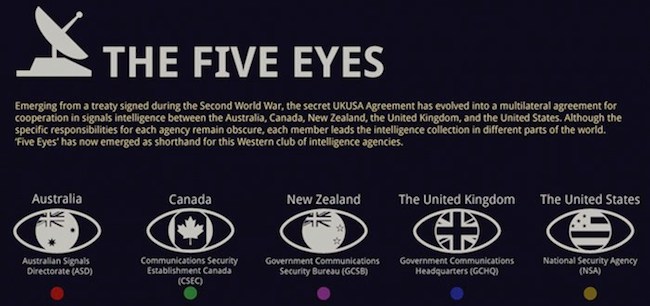
While the Five Eyes may sound like a criminal organization straight out of a James Bond film, this is no fiction. The secretive sharing of data and technology between the United States, Canada, Australia, New Zealand, and the United Kingdom has created what is undoubtedly the most sophisticated online public surveillance operation in history. In other words, if you’ve been on the internet, there’s a good chance the Five Eyes know about it.
Most regular internet users know that VPN stands for the virtual private networks that permit anonymous browsing. That, however, tends to be about as far as the knowledge goes. The Five Eyes are VERY interested in VPNs because the anonymity the technology provides makes it harder for them to do their “job” of spying.
VPNs vs the Five Eyes
Concerns about privacy laws, confidentiality, and even the legality of accessing some content gave rise to VPNs originally. This is because installing a VPN permits you to get past the geographical blocks and use websites that are supposed to be blocked in your country.
For instance, Netflix blocks most of its U.S. content to other foreign countries. Similarly, people in the United States may not be able to access TV shows and movies shown in South America. VPNs create a loophole around this sort of restriction and allow users to reach blocked websites.
It should be obvious why the Five Eyes surveillance alliance is not a big fan of VPNs. They want to know that online activity is being monitored. VPNs make it more difficult to do that.
If it seems that this organization is nothing more than a band of spies in search of questionable activity without much probable cause to rely on, you would be right. Since all five of are English-speaking countries, sharing the information they find is ever-so-easy.
History
The concept behind the Five Eyes has been around for awhile. In fact, the surveillance agreement and data sharing that form the basis of this modern arrangement were established many years ago as the UK-USA agreement that was created in 1943 during the throes of World War II.
After the Cold War ended, other countries were offered membership in the alliance, mainly as a result of efforts to deal with the growing threat of international terrorism.
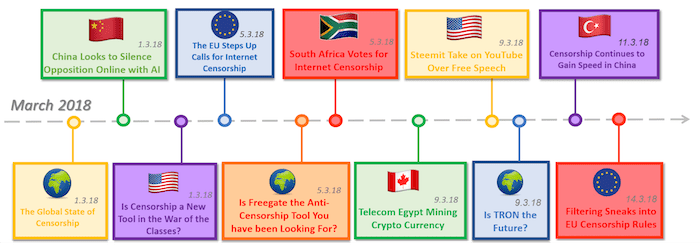
As the list of participants in the Five Eyes has grown, the extent of online global monitoring has increased as well. For a taste of the extremes to which these countries go to monitor users, check out this recounting of the expose’ of Edward Snowden in 2013.
As the work of the five countries has become more sophisticated, funding has continued to rise and the demand has been ever greater to include more security and intelligence agencies. Some of the most powerful acronyms in the world are involved, such as the FBI, CIA, NSA, MI6, ASIS, NZSIS, AGO, GCSB, and many more.
While the activities of the organization are offered up as necessary for law enforcement, it’s not hard to imagine more sinister purposes for the Five Eyes, especially as they go about the business of circumventing privacy protection laws. In case readers have forgotten, it’s against the law for the United States government to spy on its own citizens.
Thanks to the Five Eyes, it’s an easy matter to ask one of the other four countries to do it for them.
The Five Eyes is Just the Beginning
Although the agreement between the five countries may be enough to put fear into those who want to protect their privacy, this is not where the monitoring ends. In fact, there are two more alliances that increase the number of eyes as the number of countries involves is greater. But first, is Japan set to become the sixth member of the Five Eyes?
The Five Eyes Plus One: Japan in the House
The Five Eyes are presently considering the official admission of a sixth member to the world’s most exclusive spy club — Japan. It’s not such a radical step when you consider that the alliance has been able to count on Japanese cooperation dating all the way back to the Cold War. Thanks to its geographical proximity, Japan has contributed much to intelligence-gathering in mainland China, the South China Sea, and North Korea. Formal membership in the Five Eyes would simply put names on the dotted line to back up what is already a boots-on-the-ground reality.
How does the Five Eyes go about the process of adding members? It’s been awhile since they’ve done it but one head of state member simply has to make the nomination. Acceptance or rejection relies on a simple vote. With all Five Eyes countries having been on the receiving end of Japanese intelligence cooperation in recent years, most experts figure the decision is a fait accompli. Let us be the first to say “Welcome!” to the Sixth Eye.
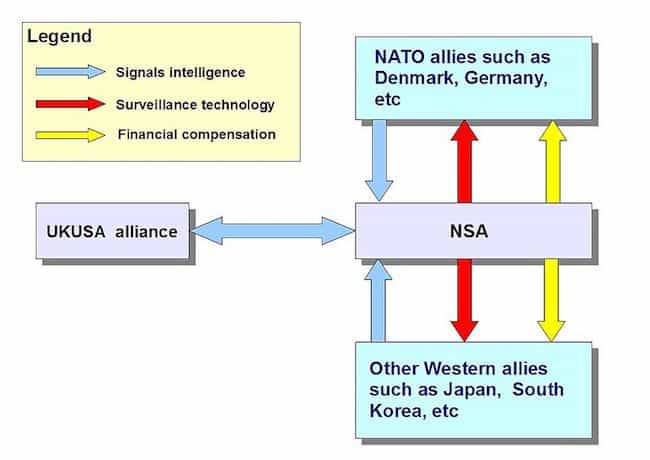
Nine Eyes
With Denmark, France, Netherlands, and Norway, the original union between the aforementioned five countries expands to the so-called “Nine Eyes” surveillance alliance. Unlike the uninspired creativity of its name, this organization possesses mind-boggling abilities that have only increased with the addition of the new countries.
Fourteen Eyes
Ultimately, adding Germany, Belgium, Italy, Sweden, and Spain helped create the final form (for now) of this alliance. With a total of 14 countries, the name of this iteration of the alliance is called “Fourteen Eyes.”

Why Should Users Care?
Although the unsupervised monitoring that occurs by these five countries is difficult to fully comprehend, why should an average user worry? When you consider that a great number of all VPNs in the world are located in one of the aforementioned five countries, and subject to those jurisdictional laws, it would be no surprise to see the practice of using a VPN come under attack.
The bottom line is that if you’re using a VPN in order to remain anonymous, that could become problematical in a Five-Eye country. At that point, privacy will be out the window and the main reason for having a VPN rendered pointless.
Protection from the Alliance
In reality, the easiest way to prevent governments from around the world from spying on your data is to use a VPN located in a different country. For instance, China is not on the list of any alliances where data monitoring is considered normal.
Thus, having a China-based VPN will make it impossible for these groups to reach one’s browsing history. That is, of course, if China does not join the group or happen to be working with them secretly.
The other alternative, which is even easier and cheaper, is to simply rely on website encryption. This can be achieved by allowing the website to engage in secure browsing. In order to confirm that it is indeed secure, one should just look for a green “https://” located on the right side of the actual URL of the website. If it is there, the content and any interaction between the user and the website are encrypted.
It is crucial to understand that there is absolutely no way to completely prevent people from accessing one’s data or browsing history. This is because it is quite literally impossible to create a system that works correctly 100 percent of the time without fail. Sorry, that’s just the reality of life.
In fact, a hacker with enough time, money, and knowledge could theoretically break into even the Pentagon’s vaunted data center. The problem, however, is that most hackers do not possess the proper combination of these three inputs. When a user encrypts his or her data, it dis-incentivizes hackers or governments that monitor online activity from trying to get in because the length of time required creates a rapidly approaching point of diminished returns.
Lastly, users could also micro-manage all of their online activity and files by looking for apps and providers that guarantee privacy. These include organizations like SpiderOak, Truecrypt, DuckDuckGo, OTR chat, and any one of a list of open-source tools which put privacy first.
If you’re looking for better online protection pleases see our recommend list of Canadian VPNS.





