Privacy Canada is community-supported. We may earn a commission when make a purchase through one of our links. Learn more.
Most Secure Browsers for Full Anonymity (2025 Update)
Are you looking for the best secure browser? If so, you’re not alone. More people are looking for ways to ensure that their online time also is private time.

However, people are now learning that they have to do more than just hide their IP address with a VPN and use a secure password manager. These days, it’s also essential to find the most secure browser.
What does secure browsing mean? It means traversing the Internet without leaving a digital footprint everywhere you roam. Just as vitally, the best secure browser ensures that no one is spying on you. Your chances of being infected with malware or a virus are reduced. If you bank or shop online, you can feel more confident about the privacy of these transactions thanks to your secure browser.
The Problem With Many of the Most Common Browsers
When a consumer purchases a new device or operating system, it comes with an Internet browser. It may have a familiar name like Chrome or Microsoft Edge.
This familiarity makes the browser seem safe. However, these pre-loaded Internet browsers aren’t the most secure web browsers that you can find.
As an example, these browsers will be configured for the ultimate in speed and accessibility. That sounds good, but these settings are the least secure. What’s more, these browsers don’t have the built-in capability to keep nefarious people and entities out of your private business.
This is especially true when the device or operating system comes packaged with other software programs. This multiplies the number of vulnerabilities, leaving you even more open to attack.
Even if you take care to visit websites that use HTTPS and SSL certificates, you can still find yourself vulnerable thanks to a browser that’s not secure.
Add to this the fact that the average consumer frequently does not know how to configure their browser for optimum security, and you have a recipe for disaster.
The answer is to choose the best secure browser that already has multiple layers of protection. It’s an easy solution that you don’t need a great deal of technical expertise to use.
| Browsers | Key Feature | Why this Browser? | Our Rating | Visit Site |
|---|---|---|---|---|
| TOR | TOR can be used in conjunction with a VPN for extra security | Easy to use | 3 ★★★★★ | Visit Site |
| Brave | Blocks ads and trackers for improved anonymity | Best Browser | 4 ★★★★★ | Visit Site |
| Mozilla Firefox | A user-friendly interface | Best secure browser | 5 ★★★★★ | Visit Site |
| Epic Privacy | No history retained | Anonymizing proxy with one click | 4 ★★★★★ | Visit Site |
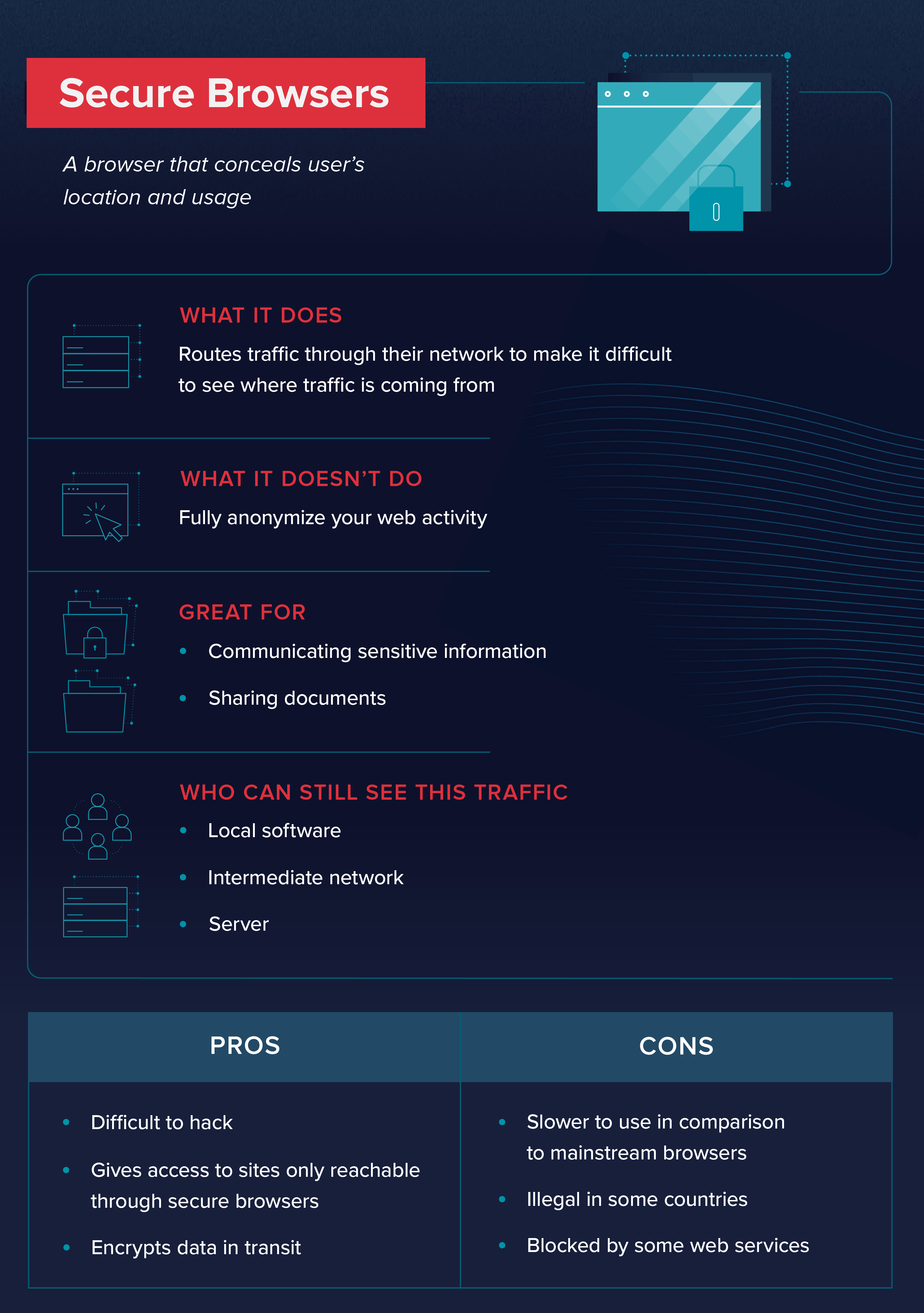
What Is a Secure Browser?
It’s important to understand that the average browser isn’t concerned with user security or privacy. Some of them sell your personal information to whoever asks for it. This may result in the user being hit with highly targeted ads. Alternatively, it also may mean that your private data ends up in the wrong hands.
Keep in mind that the average browser keeps track of a multitude of information about you. They use a geo-location app to figure out where you are in the world, and they track all of your movements on social media. Your browser even knows all about the hardware and operating system that you’re using.
If your browser has the popular WebRTC plugin, there may be additional vulnerabilities. Web Real-Time Communication is meant to streamline the process of browser-to-browser communication. However, WebRTC calls may have security issues. Thanks to WebRTC leaks, websites may be able to view your IP address and other identifying details. With WebRTC being a common plugin for popular browsers, these may not be the most secure options.
To make your online experience more secure, you can take several steps. These include keeping your browser up to date, not storing passwords in your browser, blocking popups and disabling third-party cookies. Of course, if you choose a more secure web browser, many of these steps have already been taken for you. With additional protection like tracking blockers, you’re ready for an anonymous experience.
Why Do You Need a Secure Browser?
Think about all of the things for which you use the Internet on a daily basis. Some of it’s pretty harmless and not particularly private, like searching for a new dinner recipe or learning about the environmental benefits of making your own laundry detergent.
You may not mind if your browser, ISP, your search engine and any number of strangers know that you’re interested in these topics. However, chances are good that you do much more online than just look for recipes.
If you pay bills online, look at your bank statement at the credit union website or use your credit card at a retail website, you probably want those transactions to be utterly private and secure.
Do you like to use social media? Maybe you don’t mind if the whole world sees all of your posts, but some people like to keep things more discreet. The best secure browsers enhance the possibility that you truly do have control over who has access to your social media profile.
It’s also vital that you use a reliable secure email service. Failing to do so, and failing to exercise necessary caution when receiving unfamiliar or suspicious emails, puts you at risk for phishing and other common online attacks.
Even if you feel that you don’t do anything that’s particularly private online, consider that hackers and other nefarious parties are always looking for vulnerabilities in your system. They’ll do almost anything to infect your system with malware, adware, spyware, Trojans or viruses.
Any of these programs could bring your device to its knees. Doesn’t it make sense to use a secure web browser to prevent this from happening?
Choosing a Secure Browser
Many web browsers are out there, but some of the most popular and widely used choices are nowhere close to being the most secure. However, other browsers excel at ensuring privacy and security. Here are four of them.
1. TOR
“TOR” is an acronym for “The Onion Router.” You’ll see how fitting the name is once you understand more about how it works.
Anyone who has ever cut into an onion knows that it’s made up of many layers.
The philosophy behind TOR is that many layers of encryption keep users safer. Accordingly, this is the best secure browser because it utilizes a three-layer proxy.
Someone who uses the TOR browser will have their web traffic sent through random-selection TOR relays before it reaches the requested destination. This hides the user’s actual physical location and IP address so that they can enjoy an anonymous and completely private online experience.
Pros
- It’s virtually impossible to trace web traffic that’s routed through TOR
- TOR can be used in conjunction with a VPN for extra security
- Easy to use: Just download and launch
Cons
- Anonymous, volunteer-operated servers may have vulnerabilities
- Scripts and plugins still can be exploited
- Data transfer rates can be slow
TOR is as easy to use as any of the more common browsers despite all of the more complicated processing that is taking place behind the scenes. Before being sent onto the Internet, TOR bundles your web traffic into layered, encrypted packets. It is then bounced around by a series of servers that are operated by volunteers.
At each server, one layer of encryption is removed from the web traffic. This means that each server is only aware of the prior and the next relay without necessarily being aware of the origin or the ultimate destination. This layer upon layer of complexity is what makes it all but impossible for anyone to trace your web traffic when you use TOR.
2. Brave Browser
If you hate ads, then Brave is for you.
The brainchild of well-known tech pioneers, who have worked with Mozilla and JavaScript, Brave Browser aims to be a game-changer in the industry.
It is open-source software that is based on Chromium. However, it’s unlike other browsers that have come before. That is because of its attitude towards ads.
It blocks the ads that users would normally see with other browsers, replacing these with ads from its own network, if you choose to see them. Ad trackers are utterly absent from Brave, but ads are still found among search results. Brave uses an ad-blocking extension to keep out unwanted ads, which means that each website that users visit downloads far less data, keeping speeds at a more-than-acceptable level.
Pros
- Blocks ads and trackers for improved anonymity
- Fast data transfer rates
- Plenty of extensions available on the Chrome Web Store
Cons
- Brave Rewards seems a bit convoluted
- Possible WebRTC leaks
- Ubiquitous AdWords advertisements still displayed in search results
Brave is a new entry on the browser scene, having just entered the market in 2016. With ad blocking and other technology, Brave runs pretty lean on your system, using less memory and fewer CPU cycles than competitors.
Although Brave blocks the ads that would organically appear on webpages, the makers behind the service also understand that online companies have to make money. Accordingly, users can opt into the Brave Rewards program, which awards tokens for viewing certain ads. Users then choose to award certain websites a “tip.”
Since Brave is based on Chromium, you can add more functionality simply by using the Chrome Web Store, which sells numerous extensions.
By taking trackers out of the equation, Brave makes it virtually impossible for advertisers to identify users and follow them. This definitely contributes to a more private online experience.
3. Mozilla Firefox

If secure browsing is important to you and you prefer open-source software, then Firefox is a great alternative. Not only does this provider promise a secure browsing experience, but also it is fast and isn’t a huge drain on system resources.
One of the main selling points behind Firefox is that it’s owned by a non-profit organization. This means that Mozilla isn’t particularly motivated to sell user data. Regular updates ensure user privacy, and automatic blocking of ad trackers make this an incredibly sensible choice.
Pros
- Great data transfer rates
- Accessible and effective security tools
- A user-friendly interface
Cons
- Certain legacy extensions are not compatible with the latest version of Firefox
- Customer support may be difficult to reach
- Some people dislike the frequency of the updates
With protection against malware and phishing, Firefox truly is a best secure browser. You also have access to content blocking so that it is possible for the browser to block all detected trackers. Further, a wide variety of add-ons are available for additional privacy, security and functionality.
4. Epic Privacy Browser

Secure browsing is Epic’s hallmark. Unlike many of the most common browsers, it defaults to the ultimate security settings to keep your data secure. Like Brave, Epic is built on the Chromium platform. No plug-ins are allowed and all third-party cookies are blocked.
One click is all you need with Epic to direct your web traffic through the integrated proxy server. This hides your IP address. In addition, Epic constantly broadcasts a do not track warning while also taking active steps to locate and block ad and social networks that would otherwise track online activity.
Pros
- Anonymizing proxy turned on with one click
- All traces of browser history erased upon exit
- No history retained
Cons
- Doesn’t work with password managers
- You may encounter websites that won’t run or run weirdly on Epic
- Standard search modifiers may be skipped by the search engine
Epic is as easy to use as Chrome is. It’s simply a matter of downloading and installing the program. You’ll be able to see on the home page how many trackers and third-party cookies Epic has blocked for you. Keep in mind that these stats are for your current secure browsing session only. That’s because Epic keeps no record of your sessions.
Epic even has its own search page that relies on the most-used search engines, but without leaking any of your data to those providers. This means that it doesn’t try to auto-fill what you’re typing into the search bar. All queries are routed through the proxy to keep your IP address private.
Browsers to Avoid
Choosing the best secure browser helps to keep kids and parents safe online. However, secure browsing doesn’t happen by accident.
Unfortunately, some of the most well-known web browsers aren’t secure. People may be concerned to hear that Google Chrome isn’t a secure browser, and neither is Internet Explorer. Edge and Opera also are untrustworthy.
Google Chrome is the most widely used web browser. They take steps to ensure user security. However, if you’re really concerned about privacy, you cannot trust a web browser that’s owned by a company that’s infamous for keeping and tracking data.
Despite Internet Explorer being hopelessly outdated, people continue to use it. Microsoft has migrated to the Microsoft Edge web browser, which means that the Internet Explorer isn’t getting updates. Moreover, it was plagued by security issues. Edge is hardly better. It has no blocking for trackers, and there are numerous reports of security issues.
Opera has strikes against it like opaque security settings and purchasing VPNs that are known to log customer usage. Additionally, Opera is owned by a Chinese consortium that has terrible privacy records.
Accordingly, it’s best to avoid all of these common browsers.
FAQs
Q: Can you still be traced when using TOR?
A: It’s virtually impossible for any web traffic to be traced through TOR because of its multi-layered system. This system prevents one relay that’s handling a particular packet of data from knowing anything beyond the immediately prior relay and the next relay. Even the most sophisticated trackers are unable to follow the random complexity of this system.
Q: Is using TOR dangerous?
A: TOR is a safe, reliable and private means of being online. All web traffic is sent through random-selection TOR relays on the way to its destination. This provides a great deal of privacy, anonymity and security, especially since each relay is only aware of the prior relay and the next one.
The exception to this is the exit node, which is the final relay before the request reaches its destination. This server knows the prior relay and the ultimate destination, which could be an issue if the person operating the server has nefarious intent.
Keep in mind that TOR runs on a vast system of volunteer servers that act as the relays. These relays are only as reliable as the people who own them. While the majority of them are secure and trustworthy, there is an opportunity for a criminal to obtain some private information from users.
Q: How do I prevent my IP address from being tracked?
A: Many people are looking for ways to minimize their digital footprint. ISPs, browsers, ad trackers and millions of other players do everything they can to keep tabs on where you go and what you do online. One of the main avenues for accomplishing this is through tracking your IP address.
Every device is assigned a unique IP address that identifies the user wherever they roam online. However, this data can be enshrouded in secrecy by doing things like using a secure web browser. Other measures like HTTPS and SSL also help to prevent IP address tracking, you could also substitute your IP address. All of these measures disguise your IP address and make it look like you are in a different physical location, thereby making it virtually impossible to track you online.
Q: Does Incognito offer anonymity while using Google Chrome?
A: Incognito Mode is a setting on the Google Chrome browser that purportedly provides a more anonymous session. However, this setting is mainly meant to conceal what you do from other people who may use the same device. Google and most other search engines still track your every move (Recommended: Start using a good secure search engine)
Moreover, Incognito is unlikely to hide your information from any websites that you visit, your ISP or the organization, like your employer, that has ultimate control over your network.
The only way that Incognito can work is if you choose Incognito Mode while not signed into any Google account. Once you sign in, the jig is up. Google retroactively links your account info to your recent browsing history.
Q: Does my Internet Service Provider know what I do online?
A: An Internet Service Provider, or ISP, absolutely is aware of everything that you do online. Part of their revenue depends upon it. They use the data that they collect about your behavior to send you targeted advertisements. Moreover, they will sell the data to numerous third-parties that either want to sell you something or use your private data for their own nefarious ends.Fortunately, you can keep your ISP in the dark by choosing the best secure browser available and sticking with a reliable VPN.
Final Thoughts
With the best secure browser, you’ll be able to maintain privacy and anonymity online. The most reliable providers that are mentioned here default to stringent security standards that are meant to keep you safe on the Internet. Choose any one of them to reduce your digital footprint and add an extra layer of protection by getting yourself a secure VPN like NordVPN (Alternatively, you can check out the best VPNs here).