Privacy Canada is community-supported. We may earn a commission when make a purchase through one of our links. Learn more.
What is Browser Fingerprinting?
If you’re concerned about online privacy – and you should be – you may have heard about browser fingerprinting. Browser fingerprinting allows websites and other services to immediately identify your computer, even if you’re taking several measures to anonymize your connection.
So, how do you maintain your personal privacy in this age of nosy websites? Here’s a quick, easy guide to browser fingerprinting, as well as what you can do about it.
What is Browser Fingerprinting?
Browser fingerprinting was first developed as a security measure, to allow websites to know whether someone was impersonating another user. However, the technology has been used for other, more nefarious purposes in more recent years. So, how does this work?
The answer lies in the way the internet works. No two computers are 100% identical, and websites need to know certain information to ensure that the site displays correctly. So far, so good.
However, there’s a downside to this. When all these dozens of factors are taken into account, your browser is most likely totally unique. For example, the computer this article is being written on was tested on two different services. On both services, it was totally unique.
Your browser fingerprint doesn’t just include information about the browser itself. It also includes information about your phone or computer. This means you can potentially be tracked even if you’re using several precautions, such as a VPN.
What Makes a Browser Fingerprint Unique?
So, what goes into a browser fingerprint? As we mentioned, this fingerprint includes information about both your browser and your computer. Here’s some of the information that makes up your browser fingerprint.
Headers
When your browser connects to a website, there are a number of headers embedded in the information it sends. All of these headers combined will give the website vital data about how it should relate to your system. In all, there are 8 different headers that your browser sends. These are:
- The language header. This header lets the website know what language your computer uses (English, Spanish, etc.).
- The referrer header. This header is present if you’re clicking a link from one website to another. It lets the second site know how you got there.
- The cache–control header. The cache-control header instructs the website how data should be cached, both on the client side and the server side.
- The user agent header. This header is present on every web connection, and tells the website what browser and operating system you’re using.
- The accept header. The accept header lets the website know what kinds of content your computer and browser are able to display.
- The content–encoding header. This header gives instruction on what kind of compression your browser is able to handle.
- The connection header. The connection header determines whether your connection to the website remains open after the current connection, or whether it should be closed.
- The upgrade insecure requests header. This header tells the server whether your browser is requesting an encrypted connection.
As you can see, these headers contain a lot of information. In many cases, the headers alone are enough to provide a unique fingerprint for your browser. However, there’s additional browser information that websites can also access.
Additional Browser Information
In addition to headers, your fingerprint includes the build ID of your browser, which tells the website what exact version of your browser you’re using. A secure browser will obscure this information.
Your fingerprint also includes a list of plugins supported by your browser. For example, if your browser supports JavaScript but not Flash, this information will be included.
Various ad preferences are also part of your fingerprint. These include your cookies settings, Do Not Track preferences, and whether or not AdBlock is installed.
Finally, your fingerprint contains two different images. One is rendered by your browser’s HTML Canvas element, and the other is rendered with WebGL. Since different systems will generate slightly different images, these images can help identify your computer.
Information About Your Computer
As already mentioned, your browser fingerprint includes information about your phone or computer as well as the browser itself. This includes the audio and video formats that are supported, as well as what fonts are installed.
In addition, websites also collect information on your time zone, as well as your monitor resolution and color depth. This information is needed to serve you the correct content, but it can also be used to identify you.
Why Is Browser Fingerprinting Being Used?
Now that we know what goes into a browser fingerprint, it’s time to talk about how it might be used. There are four primary reasons. Two are good for you, and two are bad.
Good Reason #1: Preventing Financial Fraud
Browser fingerprinting has been used for years by the financial sector. It’s used by almost every online banking service. By fingerprinting your device, the bank can determine whether a browser session has been hijacked, and shut down fraudulent transactions.
Similarly, browser fingerprinting is often used to prevent credit card fraud. For example, if you use your card regularly online, a website can identify when it’s suddenly being used on a different device.
Good Reason #2: Preventing eCommerce Fraud
Similar to preventing credit card fraud, browser fingerprinting can be used to combat a variety of eCommerce fraud techniques. Wire transfers and other payment methods typically come from a predictable source. Along with other factors, a sudden change of device can indicate fraud.
Bad Reason #1: Analytics and Ad Tracking
Our digital economy depends in part on online advertising. The good news is that you can get all kinds of online content for free. The bad news is that you might not want to be tracked in this way.
Ad services used to track customers via cookies, but many people have gotten savvy. With so many people disabling cookies on their devices, advertisers needed a new way to track individual customers. Many of them have turned to browser fingerprinting as an alternative.
Bad Reason #2: Malicious Websites
Browser fingerprinting is resource-intensive for servers. Most websites would rather use a traditional tracking method. In fact, one study showed that only 0.4% of the top 10,000 websites use browser fingerprinting. Most of these are financial websites.
The same study also found that the majority of sites that use fingerprinting are either spam websites or malicious sites. In other words, your browser is more likely to be fingerprinted by cybercriminals than by a legitimate website.
How to Check Your Devices for Browser Fingerprinting
So, how do you know if your browser’s fingerprint is unique? There are two main services: AmIUnique, and the Electronic Frontier Foundation’s Panopticlick service. Both of these services are well-regarded, but there are a few key differences.
Panopticlick uses only the most commonly-used fingerprinting methods. These include headers, browser version, time zone, and other methods that are less resource-intensive.
Amiunique uses all of these methods. However, they also use WebGL and HTML Canvas drawings. In addition, they provide global statistics, so you can see how your results compare to all of their other users.
Keep in mind that neither of these services are perfect. They can give you some ballpark numbers, but they face two limitations.
First, there’s the issue of sample size. Simply put, if none of their users share your browser’s fingerprint, you might show as “unique” even when you’re not. You’re just unique among users of that particular service.
Second, they have a lot of outdated data. In most cases, this is a non-issue, but it can be deceptive when it comes to browser version and OS version. Since these sites have been around for years, and your particular browser version has probably only been available for a few months, it will probably show as rare, even though it’s likely common.
How to Protect From Browser Fingerprinting
So, how do you protect yourself from browser fingerprinting? The short answer is that there’s not one single preventative measure. But there are several methods that, when combined, can offer significant protection.
Use a VPN
A VPN, or virtual private network, is a tool that creates a secure connection between your computer and the VPN’s server. From there, the VPN server connects to the web.
A VPN, by itself, will not totally prevent browser fingerprinting. However, it can obscure a lot of information. For example, if you connect through a VPN in a different time zone, that information will be different.
Not all VPNs are equally useful. For example, you should avoid using a free VPN. Most of these are avoidable scams, and will either serve up extra ads or steal your information. A quality paid VPN will cost a few bucks, but you can rest assured that your connection is safe and secure.
Use Anti-Malware

To begin with, everybody should be using anti-malware or antivirus protection. It’s just common sense. Not only can anti-malware protection protect you from nasty computer bugs, they can also help obscure your browser fingerprint.
Please note that your built-in virus protection isn’t going to cut the mustard. Products like Malwarebytes and HitmanPro will provide the level of protection you need, preventing the installation of harmful software that depends on your browser fingerprint.
It’s important to keep in mind that anti-malware software is constantly being updated to keep up with the latest online threats. Make sure to enable automatic updates to ensure that your protection is up to date.
Disable JavaScript
Disabling JavaScript is an effective way of obscuring your browser from being fingerprinted. The reason is that without JavaScript enabled, websites can’t detect what plugins and fonts you have installed. Since this information is a major part of your fingerprint, it’s a good idea to prevent websites from seeing it.
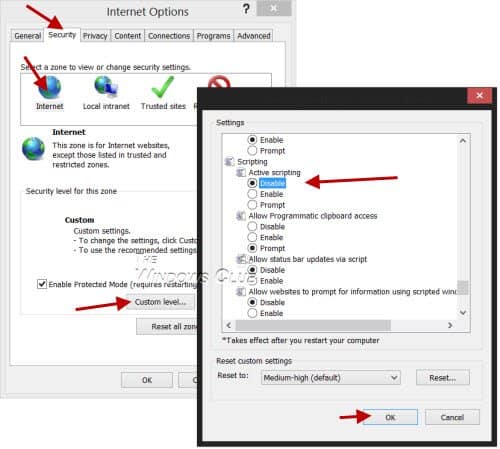
That said, many sites require JavaScript to operate effectively, so you might be throwing the baby out with the bathwater. But what if you could get the best of both worlds?
One solution is to use a tool like NoScript. NoScript will block JavaScript on all sites by default, but allows you to enable it for the sites you really want to use. The downside is that this has to be done manually, so it does require a little bit of work to be used effectively.
Use Incognito Mode
Many browsers have an “Incognito Mode” that obscures many browser details. Essentially, what this does is set your headers and browser profile to preset choices. Because all Incognito Mode browsers look the same, websites will need to rely on computer hardware data to try and fingerprint you.
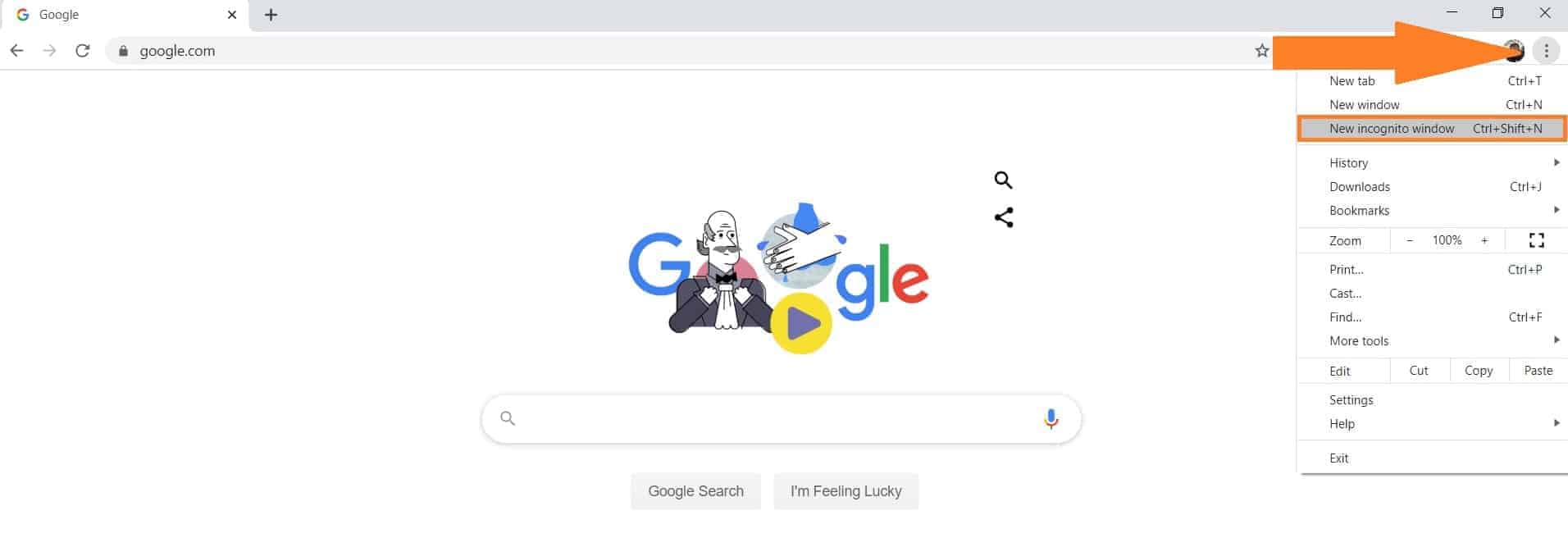
Incognito Mode is supported on Safari, FireFox, Chrome, and several other browsers. Use it while you’re browsing, and you’ll be significantly harder to track.
Use the Tor Browser
Tor Browser is a project that’s designed to promote maximum privacy. Instead of connecting directly to a website, you connect through a Tor “node”, which is another Tor user. Your connection is routed through several nodes in order to obscure your identity.
In order to further mask your browser fingerprint, the Tor Browser standardizes several aspects of your browser. For example, it restricts fonts to a few select options, and it doesn’t permit HTML Canvas rendering unless you specifically approve it each individual time. It also blocks JavaScript.
The downside of the Tor Browser is that it tends to be slow. This is because your connection is routed through several other nodes. In other words, it’s a non-starter for watching videos. But for reading plain text, it’s a solid option.
Other Browser Options
So, what do you do if you don’t want to deal with Tor’s slow speeds? Thankfully, there are a few options if you want another choice.
For Windows and Android Users
In the first Firefox release of 2020, Mozilla introduced fingerprint blocking. It does this by blocking requests from sites and companies that are known to participate in browser fingerprinting.
By default, this feature is turned off, since it can prevent some websites from loading properly. That said, you can enable it on Firefox’s Privacy and Security page. Mozilla is working on enabling fingerprint blocking by default, but they have not announced a release date for this feature.
This year, Google also announced that they would introduce fingerprint blocking in Chrome. However, no release date has been announced. That said, you can get some measure of protection for your Android device by using an Android-compatible VPN.
For Apple Users
Fingerprinting protection has been used in Apple’s Safari browser since last year. If you’re running the latest version of iOS, fingerprinting protection will automatically be enabled. This option is only available on iOS devices, so PC users will need another option.
Safari’s fingerprinting protection works by sharing only the information that a website needs to run. This isn’t 100% effective, depending on what the website claims to need. But it can protect you from most bad fingerprinting while still allowing for desirable fingerprinting such as your banking site.
To get better protection, make sure to use an iOS VPN that will obscure other information, such as your time zone.
Browser Add-Ons
There are other ways to prevent fingerprinting, as well. For Chrome users, you can download Disconnect, which automatically disables tracking. On some sites, particularly shopping sites, it can cause issues. But you can temporarily disable it with the click of a button.
Firefox users can install Canvas Fingerprint Defender. This is a bit more comprehensive than Firefox’s built-in anti-fingerprinting tool. However, like Defender, it’s also been known to cause issues on some sites.
Use the “Do Not Track” Option
Do Not Track is a request that can be embedded in your browser’s header. It’s exactly what it sounds like: it requests that websites don’t track you. Because it’s part of your header, not a cookie, it will remain in place even if you clear your cookies.
Most browsers, and all major browsers, support the Do Not Track header. Simply open your browser’s settings and see if it’s enabled. With this header enabled, you can tell your ad blocker to accept ads from sites that respect the Do Not Track header.
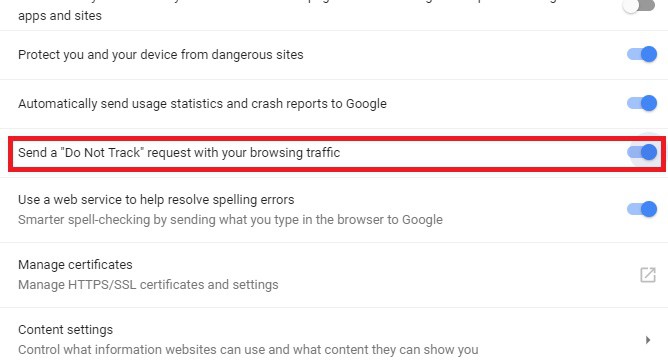
Most websites ignore the Do Not Track header, which is unfortunate. So how does this help? In the short term, it doesn’t. However, it allows you to support sites that respect your privacy, while still blocking ads on sites that track you.
In the long term, if enough people use the Do Not Track option, websites will see the advantages of respecting it. Providing this kind of financial incentive is the best way to get online advertisers to change their ways.
Conclusion
As you can see, browser fingerprinting is a complex issue. To begin with, it has many beneficial security applications. In other words, if you could completely prevent it in all cases, you wouldn’t want to. On the other hand, browser fingerprinting allows for invasive ad tracking, as well as tracking by malware sites.
For the privacy-conscious individual, the solution is to selectively enable tracking on banking and eCommerce sites. For all other applications, it’s best to use the slew of measures we outlined to prevent fingerprinting.