Privacy Canada is community-supported. We may earn a commission when make a purchase through one of our links. Learn more.
Playfair Cipher

Invented in 1854, by Charles Wheatstone, the Playfair cipher was the first diagram substitution cipher created. The cipher takes its name from Lord Playfair who promoted the use of the encryption technique in telegraphy.
Rather than a simple substitution cipher where letters are substituted for encrypted letters, a diagram substitution cipher encrypts blocks—two or more letters— at a time.
The Playfair cipher encrypts pairs of letters, called bigrams. This technique offers more security and is simple to use. The receiver of a ciphertext encrypted with the Playfair cipher only needs paper and pencil to figure out the plaintext making the cipher quite practical for telegraphy.
Due to this, the cipher was used extensively by the British in World War I and the Second Boer War. Australia also used the cipher throughout World War II.
Although the cipher is not unbreakable, by the time a cryptanalyst could break the cipher, it would likely be too late to get any use out of the message. Thus, it wasn’t used for mission-critical messages but rather for important information that still deserved encryption.
Today, Playfair is not secure thanks to digital encryption devices which can crack the cipher within microseconds. Nonetheless, the Playfair cipher holds an important role in the history of cryptography.
Cipher Example
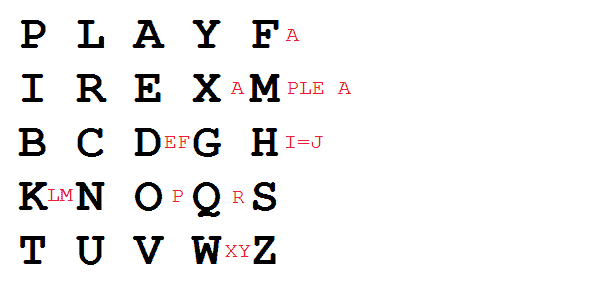
The Playfair cipher encrypts plaintext with the aid of a 5 x 5 table that contains a keyword. The keyword is placed first in the table going from the top left to top right down to the second row and across the row. If there are two of the same letters in the keyword, the second instance is omitted.
The rest of the table is filled out with the rest of the letters of the alphabet. To ensure all letters are included, I and J are used together.
Now, for someone to use the Playfair cipher to encrypt plaintext, they must know the following rules.
- If the two letters being encrypted are the same, you need to add an X after the first letter. Then, you can encrypt the new resultant pair.
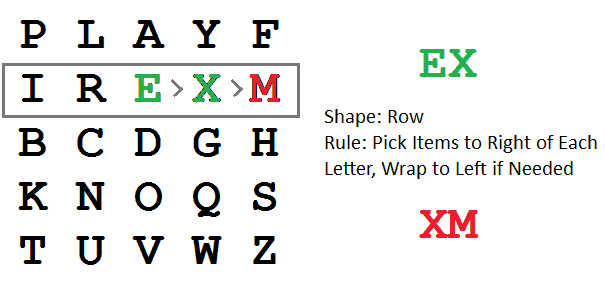
- When your letters are on the same row in the table, you need to replace them with the letters directly to the right of each, respectively. If one of the letters is at the end of the row, wrap around to the next row, and use the letter on the furthest left.
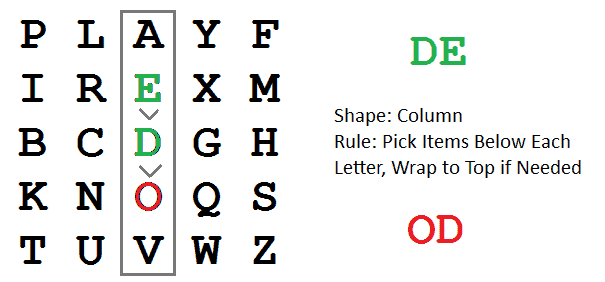
- When your letters are in the same column, you need to replace them with the letters directly below each, respectively. If one of the letters is at the end of the column, wrap around to the top of that column and use the uppermost letter.
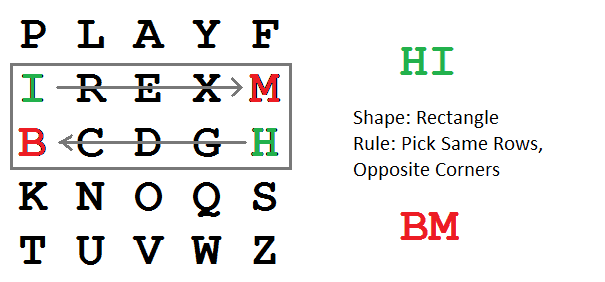
- When your letters are not in a row or a column, you need to create a rectangle with the original pair and replace the plaintext letters with those in the opposite corners.
As an example, we can use the phrase “Playfair example” as the keyword. As several letters are used more than once in the keyword, we’ll have to replace them with Xs.
Now, to encrypt the message “hide the gold”, we’ll do the following.
For the pair HI, we see the following rectangle created. The new pair, BM, is highlighted in red.
For the pair DE, we see that D is used as a plaintext character and a ciphertext character, thus it’s marked in green. The new pair becomes OD.
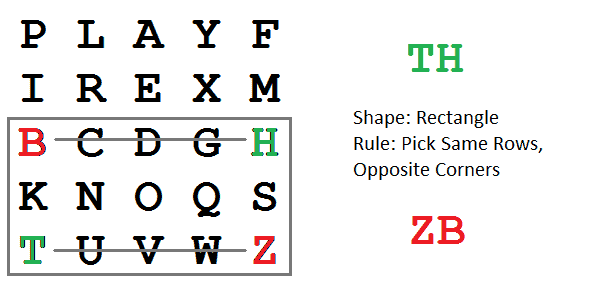
The next pair, TH, creates the following table. The new pair becomes ZB.
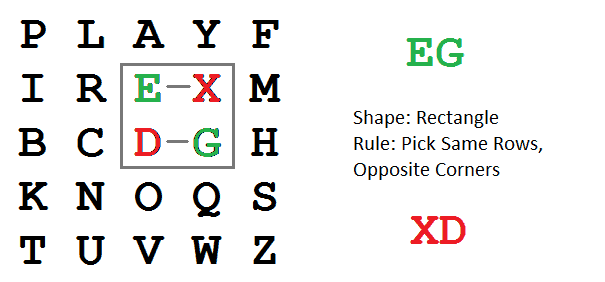
The pair, EG, creates the following table. The new pair is XD.
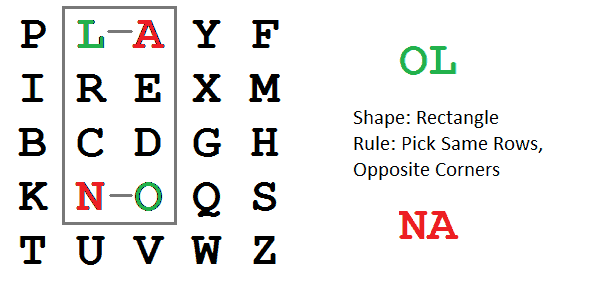
The second to last pair in the plain text, OL, creates the following rectangle. The resultant new pair is NA.
Now, only one letter remains, so we must use the letter X as an addition to create the pair DX. The new pair comes out to be GE.
Thus, the ciphertext is BM OD ZB XD NA GE.
Implementing With Python
For those interested in trying out the Playfair cipher with Python, you can use pycipher.
You must first import Playfair. Then, run the following.
Playfair(‘playfaiexampler’).encipher(‘Hide the gold’)
Playfair(‘playfaiexampler’).decipher(‘BMODZBXDNAGE)’
Cryptanalysis
If you know the plaintext and the ciphertext, finding the key of the Playfair cipher is relatively simple substitution cipher. However, when you don’t know the plaintext, finding the key is much more difficult.
The easiest way to crack the cipher is to guess words in plaintext to reconstruct the key.
As the Playfair cipher is more complex than a standard substitution cipher, cryptanalysis is more difficult. By hand, you can try to use reversed digraphs to decrypt letter patterns. In English, several words contain reversed digraphs such as the word “departed”.
Finding reversed digraphs in the ciphertext and creating a pattern of plaintext words can help guess further plaintext words to then help generate the key.
The Bottom Line
The Playfair cipher is a great example of how cryptography was used in the world. Today, the cipher offers no protection as computers can easily crack the cipher.
If you’re worried about your online security, check out the Online Privacy Guide from Privacy Canada.