Privacy Canada is community-supported. We may earn a commission when make a purchase through one of our links. Learn more.
Baconian Cipher
Devised in 1605 by Francis Bacon, the Baconian Cipher is a substitution cipher. More specifically, it’s a type of steganography, where a message is encoded within another message.
As true with virtually all substitution ciphers, the Baconian Cipher is not one to be used for security measures in the modern world. Substitution ciphers can be broken easily using basic cryptanalysis methods.
However, that doesn’t take its utility away from being able to encrypt basic messages.
Algorithm Details
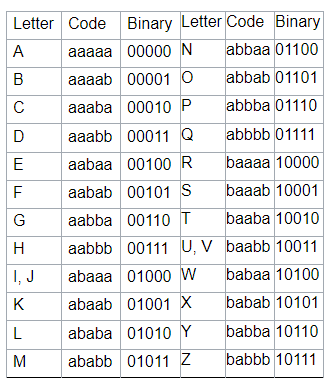
When using the Baconian Cipher, you must assign 5 binary digits to each letter of the alphabet. Most often, people use A’s and B’s to signify 0 and 1. Historically, people will use the same 5-digit binary string for I and J and for U and V, as they follow the classical Latin alphabet. This is shown below:
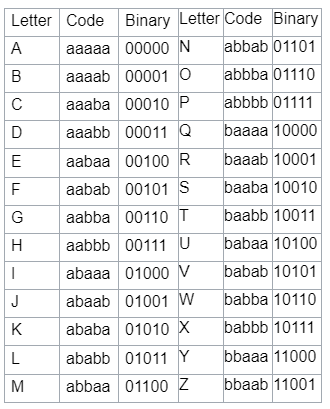
Alternatively, you can use an encoding that allows for separate values for I and J and U and V. This is seen below:
From there, you must utilize two different typefaces to represent what should be an A and what should be a B. Francis Bacon suggested using capital letters and lowercase letters to distinguish between the two. Another option is to use boldface text and normal text.
Example
If we wanted to encipher the message Francis, using the classical Latin alphabet and upper case and lower-case letters, we would replace each letter as follows:
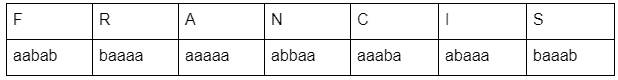
From there, our encrypted message could be the following, where a is lowercase and b is uppercase. Additionally, as there are 7 characters in Francis, and each letter is 5 digits, we know the encrypted message will be 35 characters long.
The Bottom Line
As noticeable above, cryptography is not very secure. Using two typefaces and A and B characters is quite basic. This simple substitution cipher is thus easily broken.
If you’re interested in security, such as secure emails, check out more from Privacy Canada!





