Privacy Canada is community-supported. We may earn a commission when make a purchase through one of our links. Learn more.
Cybersecurity AI vs Malware AI: Who Wins?

AI, also known as Artificial Intelligence, is a method where machines demonstrate their intelligence by mimicking human-like tasks. They are programmed to learn from experiences, eventually making their own decisions and taking action.
Every time we use social media or log into our banking app, AI is running in the background. It is constantly absorbing the actions we take in order to learn and perform better.
AI has been introduced into the area of cybersecurity because of its ability to quickly verify information and protect large networks of data. However, cybercriminals are using the same tactics to infiltrate hospitals, governments, and other corporations’ sensitive information.
Can cybersecurity AI beat out malware AI techniques?
In this article, we discuss both methods and see which one comes out on top.
Cybersecurity AI Businesses
Organizations, regardless of size, store, retain and process a large amount of information within their servers. Experienced and well-trained programmers are needed to protect such sensitive data and using cybersecurity AI is an approved method.
Since there is a rise in malware AI attacks, many businesses have popped up that specialize in cybersecurity. Here is a short list of what they offer.
Cisco
Known for its services for security products, Cisco provides solutions for email security, authentication, and quality VPNs (Virtual Private Networks).
IBM
International Business Machines, also known as IBM, protects mobile and PC products and detects threats using AI and cloud platforms.
Microsoft
Widely recognized as a developer of personal computers, Microsoft has been classified as a business that detects cybercrime. Their cloud-based platform, Azure, includes multi-factor authentication and machine learning (ML).
Cybersecurity AI businesses are becoming essential for businesses around the world.
The tools and services these businesses provide are essential and becoming a leader in the protection and safety of the data and networks of companies around the world.
Cybersecurity AI in Marketing
Another area that cybersecurity AI is expanding in is marketing. Many businesses have adapted AI algorithms into their marketing strategies to increase their sales and are seeing positive results.
Shopify, one of the most popular eCommerce platforms, is just one of many companies that use cybersecurity AIs in their apps and products. They walk you through the four steps (Start, Sell, Market, and Manage) to increase the growth of your business on their platform. One of its tools, Kit, functions as a virtual assistant for its merchants. It studies the habits of their visitors and determines what kind of posts to send on social media and customizes email marketing campaigns.
AI marketing is a growing method for many organizations and it uses at least three cybersecurity standards: Authentication, Authorization, and Encryption. The following briefly explains what each one does.
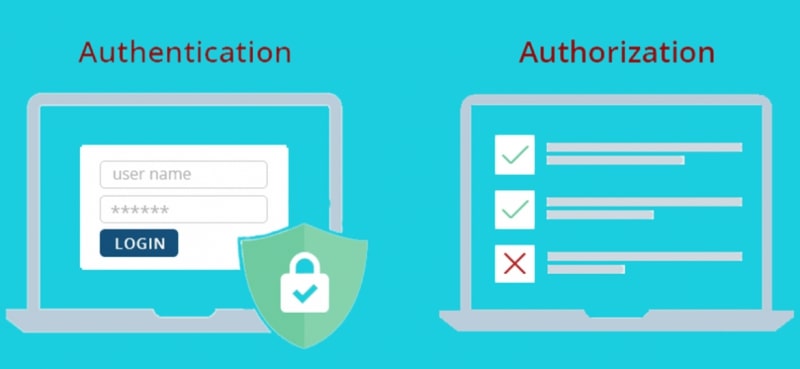
Authentication: A form of verification
When a person logs into their bank using an app, WordPress blog, or PC, it is a form of authentication. The system needs to verify a specific set of answers given to allow that person access.
Authorization: Permission to use
Payment transactions and permission to enter paid online courses are a couple of examples of authorization. Once the required information has been entered and authenticated, the system decides what kind of access the person has once approved.
Encryption: Transforming content

PDF documents, emails, and text messages are some examples that can be encrypted. These sets of data have to be encoded and modified to be transmitted easily across the web. It’s also necessary to prevent cybercriminals from getting access to the information inside.
Artificial Intelligence relies on these three essential parameters, as well as others, to assist companies with their marketing strategies. Its ability to study a person’s interaction with a site and their activity on various social media platforms gives businesses an edge in increasing their profits.
We’ve just seen the good that AI can do for companies and marketing. However, there are dangerous groups of people who use their programming talents to invade networks and servers to cause a lot of damage. In this final section, we discuss solutions to thwart such attacks.
Malware AI and How to Prevent It

One of the three credit bureaus, Experian was hacked along with a large credit card distributor, Capital One where personal data of millions was affected. There were protocols in place to protect their data but hackers were able to break in and cause damage.
Malware attacks are on the rise every day.
These two are examples that demonstrate the actions cybercriminals use to infiltrate businesses. Malware AI attacks are growing every day and companies need to use as many cybersecurity AI tactics as possible.
Malware AI learns at the same rate and speed as normal AI but causes a great deal of destruction. As it accelerates through servers and networks, it leaves behind viruses that can block out users from their accounts.
Using the right developers and security measures to prevent an attack is essential to protect sensitive data. However, cybersecurity AI can’t protect information from human error.
Outside of ransomware, which you have to install and download intentionally, phishing is one of the main tactics cybercriminals use to get access to a person’s sensitive content. They are emails that are made to look like a trusted source but are filled with fraudulent links that ask for personal details. There are a few ways to not fall for phishing schemes:
Poor Language
Most scammers have misspelled words and use poor language in their emails. A legitimate company checks its spelling before sending it out.
Requesting Personal Information
There is never a reason for a company to ask for your password, social security number or any other personal information. Unless you contact a company directly regarding a specific matter, you should not give out any of these details.
Simple passwords are another human error that needs some attention. Some people like to use their loved ones’ birthday as a password. Others use consecutive numbers and some use the word “password”. With a little knowledge and time, a person’s account and details could be accessed and spread across the dark web.
A good suggestion is to use a mixture of acronyms for names and places and incorporate numbers and symbols. Passwords should look like code that’s difficult to decipher. Using quality password managers is another great example of good cybersecurity practice in your business.
The Bottom Line
Cybersecurity AI, which utilizes authentication, authorization, encryption, and other security measures, has been beneficial to businesses in regard to data protection and marketing. There is still some risk for malware attacks but anti-cybercrime companies are constantly improving their technologies to keep information safe.