Privacy Canada is community-supported. We may earn a commission when make a purchase through one of our links. Learn more.
Back to Basics: Programming Security For Beginners and Veterans Alike
Sometimes even the best of us can benefit from going back to basics, and reminding ourselves of the core principles of what we do.
If you’ve been programming for a while, and particularly if you are self-taught, you’ve probably developed a series of ‘shortcuts’ and obtuse acronyms that only you understand
Not only is that a problem when it comes to showing someone else how your code works, it’s also a huge security risk.
Though there are some great ways of sharing code securely, if the code you write is insecure this will affect everyone else who makes use of it.
This, in fact, is one of the biggest open-source security risks, and one of the major reasons why some developers avoid open-source code altogether.
And though writing secure code is a complex art form in itself, there are some basic principles that can dramatically increase the security of every piece of code you write, whether you’re a fresh, newbie programmer or a seasoned pro. In this guide, we’ll take a look at them.
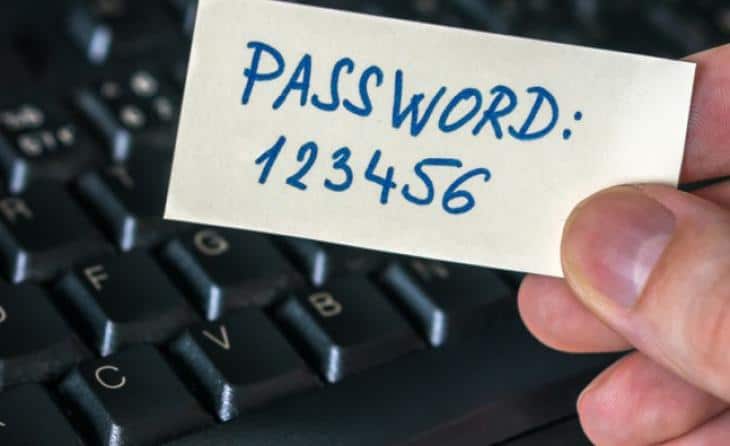
Don’t Trust The User
First and foremost, don’t rely on the user to keep themselves secure. Ever. Users are notorious and ingenious when it comes to getting around the security measures you’ve put in place for their benefit, and given half the chance to sabotage themselves will choose “123456” as their password.
Not all users are completely unaware when it comes to cybersecurity, of course. But sometimes it is the smartest, most well-informed users that are the worst security risk. If you’ve put in place sophisticated security that relies on verifying a user’s IP address, you should be aware that it might change every time they access your software since so many people hide their IP by using a VPN.
Thanks to the growing hacker problem and a massive advertising push by the industry, Quality VPNs are becoming the equivalent of virus protection. In other words, almost everybody uses it.
Before implementing and choosing a VPN, look at your security needs. You may find that you need double data encryption, data leak protection, or maybe access to a global selection of servers. In comparison testing, NordVPN ranks high in these areas. If being Netflix-ready is an important feature, you might choose a different provider. The bottom line is to take the time to do the proper research.
Despite this, programmers continue to trust their users not to open themselves up to cyberattacks. Of the OWASP top ten list, which highlights the most common and dangerous web application vulnerabilities, four – Injection, XML External Entities, Cross-site Scripting (XSS), and Insecure Deserialization – come from trusting the user too much.
In short, don’t let the user do anything they shouldn’t be able to do, even if doing that thing would be stupid.
Keep It Simple
Simple code is the most secure code. This is true in at least two senses. The first is that if you can quickly scan your code and see how it works, you are much less likely to overlook potential security holes.
The second is that, if you are sharing your code with other developers, they need to be able to understand (and adapt) it without introducing vulnerabilities.
If you want to see some examples of what not to do, take a look at The Daily WTF, which chronicles the dangers of over-complicated code. Many of the examples there point to a broader problem: that whilst the individual elements in your software are secure in themselves, the way in which they interact might not be.
As CodeXCoder has noted, running unused plugins on WordPress or any other web host is still one of the largest sources of vulnerability for the average programmer.
Automation Is Great
Too often, programmers see security as something that they can add on to their software after it is completed. For coders thinking in this way, security becomes a real burden, rather than an inherent part of their development process. As SimpleProgrammer has argued, that mindset needs to change.

A good way of simultaneously improving your efficiency and your security is to embrace automation. Whilst some grizzled old programmers will tell you that automating code generation can introduce security vulnerabilities, in most cases you can ignore them. That’s because, in most cases, security holes come from human error.
Automating your processes also has another benefit: you have more time to check your code for security holes because you are spending less time actually writing the stuff.
Threat Model Your Software
The idea of ‘threat modeling” can be intimidating for new and experienced programmers alike. The way that the term is used by high-end cybersecurity firms, the practice looks like an incredibly complicated process, utilizing AIs and advanced statistical techniques.

In reality, and when done properly, threat modeling is a process that most (good) programmers do on a frequent basis anyway. If you’ve never done it before, the basic steps are to document how your software functions, and how data flows through it. Then you can identify any step in this system at which data can be stolen. You can then improve the security of that process.
If that sounds familiar, it’s because threat modeling is a very similar process to the basic way that software is developed anyway.
Encrypt Properly
Encryption is a powerful way of securing your software, but when used incorrectly it can do more harm than good.
Encryption can be a great way of reducing backup system vulnerabilities, for instance, but only if you don’t store the encryption key in the same place as the data it encrypts, and especially not if you hard-code the key into your software.
Avoiding these mistakes is easy enough if – like in this guide – you go back to basics and learn the common mistakes that coders make when using encryption.
Programming Is A Process, Not An Event
Finally, take an “evolutionary” approach to your code. New threats emerge all the time, and you need to keep on top of them in order to make sure that your beautifully written code stays secure.
In practice, this means that all of us should return to the code we wrote years ago, and make sure that it has not become obsolete. In doing so, you might be able to laugh at some of the mistakes you made when you were new to programming. Just don’t be tempted to “improve” the code by merely making it more complicated. Trust us: get the basics right, and everything else will be fine.